
Updated Mar 30, 2026
Is My Talking Tom Friends Safe for Kids? Risks and Guardrails
A practical safety review of My Talking Tom Friends: in-app purchases, ads, notifications, privacy, and time. Includes guardrails and an incident plan.
Read article
Knowledge Library
Explore account recovery, cyber safety, platform security, and incident response guidance from Hacked.com.

Updated Mar 30, 2026
A practical safety review of My Talking Tom Friends: in-app purchases, ads, notifications, privacy, and time. Includes guardrails and an incident plan.
Read article

Updated Mar 30, 2026
Reddit safety depends on communities, DMs, and exposure to adult content. Reduce risk with strict chat settings, identity hygiene, and an allowlist of moderated
Read article

Updated Mar 30, 2026
A practical risk checklist for TikTok: content exposure, contact risk, privacy settings, scams, and time. Includes guardrails and an incident plan.
Read article

Updated Mar 30, 2026
How cyber operations reportedly supported the 2026 Iran strikes: sensor exploitation, telecom shaping, comms disruption, and influence through apps and.
Read article
Updated Mar 30, 2026
Headlines change slowly. Your account security can change today. Use this checklist to secure email, stop password reuse, reduce phishing risk, and make.
Read article
Updated Mar 30, 2026
Endpoint security tools have deep access. Use this framework to evaluate vendor dependency and reduce single points of failure with practical controls.
Read article
Updated Mar 30, 2026
AI will automate legal tasks, but security and integrity decide outcomes. Learn procurement, confidentiality, and evidence controls for legal AI workflows.
Read article

Updated Mar 30, 2026
Learn how Linux ransomware typically spreads, what to harden first, how to build reliable backups, and what to do if you suspect infection.
Read article

Updated Mar 30, 2026
Macs are not immune. Most Mac compromises come from phishing, risky downloads, and outdated software. Use this hardening checklist for accounts, browsers, and.
Read article
Updated Mar 30, 2026
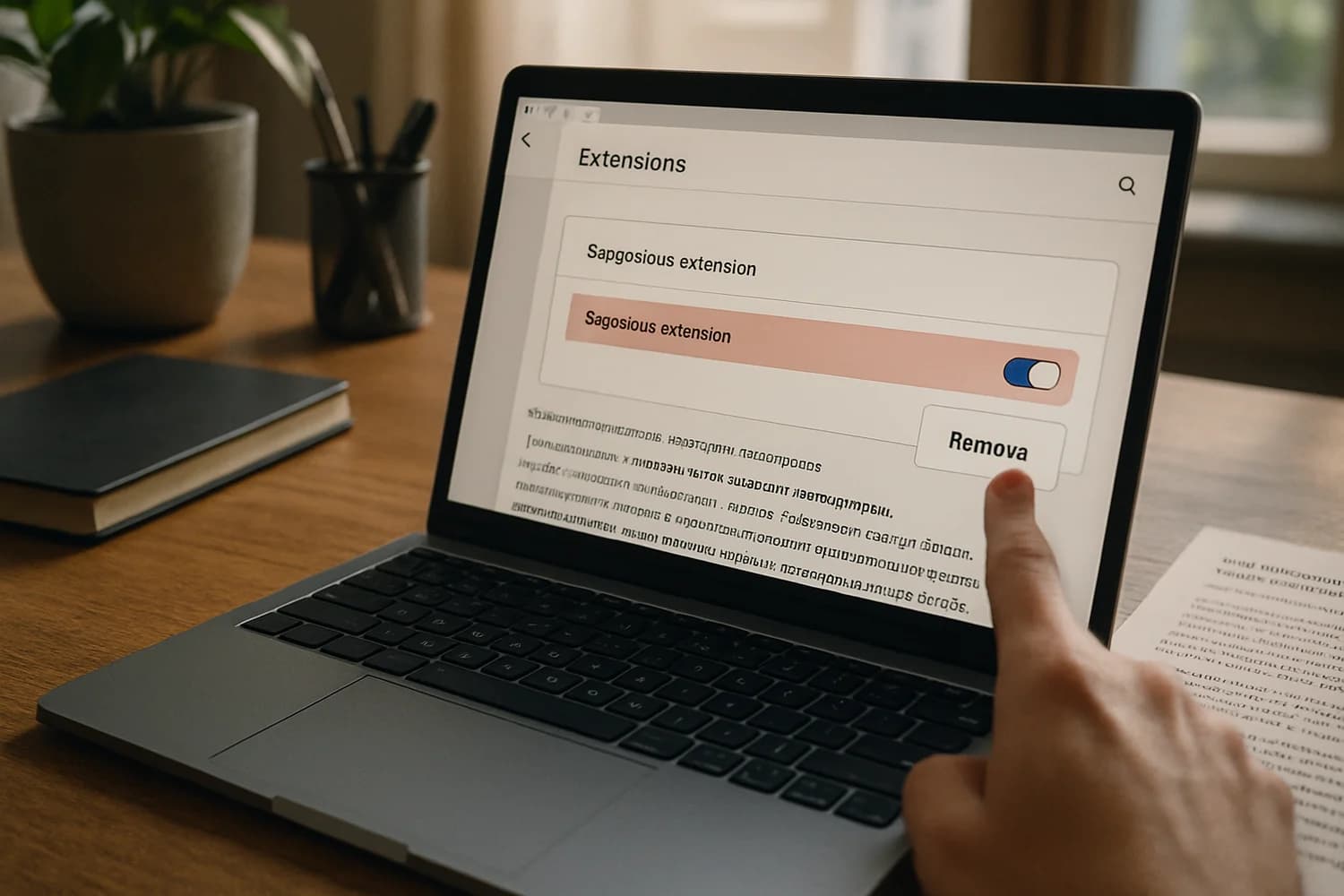
A malicious browser extension can steal passwords, session cookies, and email content. Learn how to remove risky extensions, revoke sessions, and recover safely
Read article
Updated Mar 30, 2026
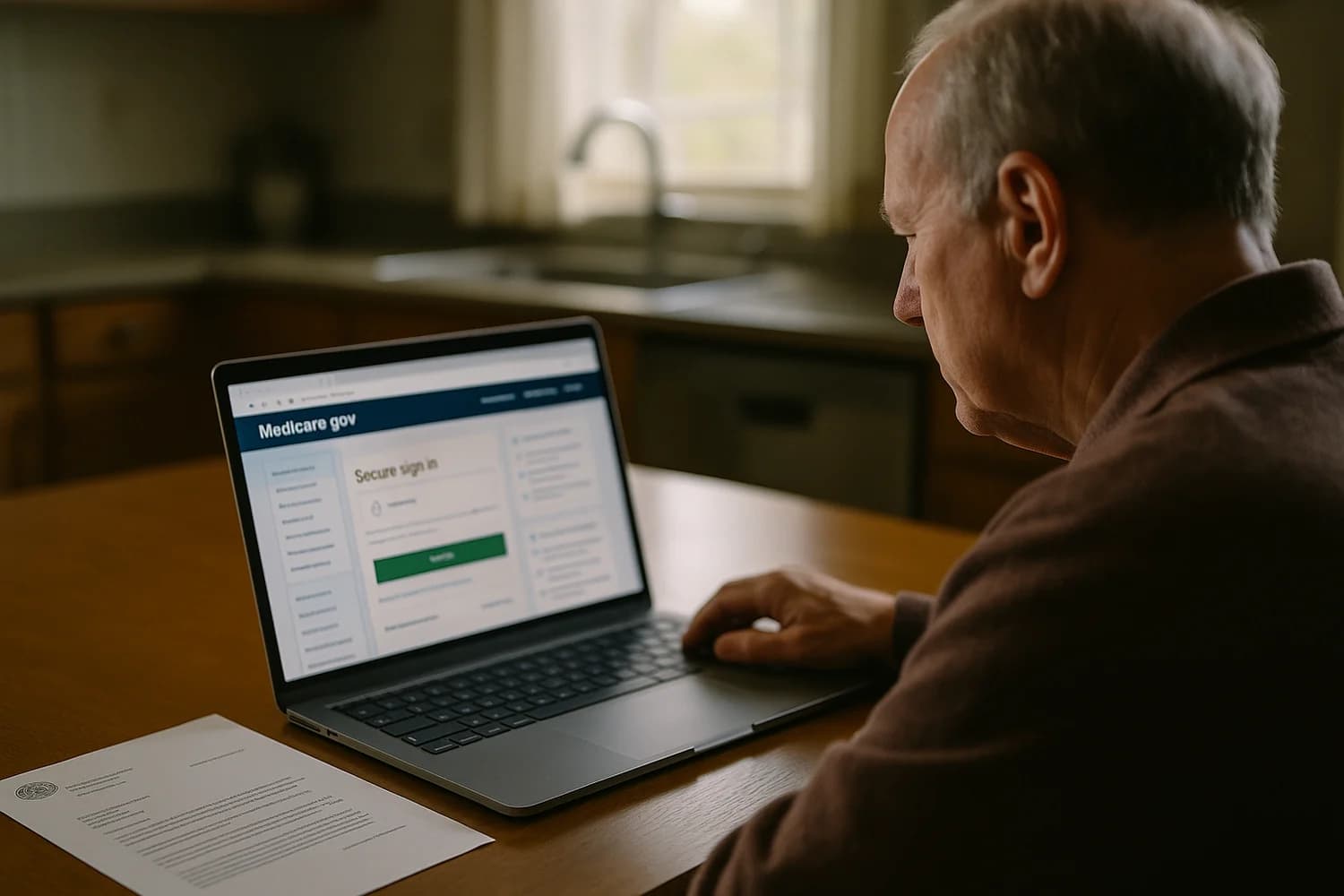
If someone created a Medicare.gov account in your name, use this recovery plan to secure access, review claims, and report Medicare identity misuse fast.
Read article
Updated Mar 30, 2026
Dating app breaches increase phishing and extortion risk. Change reused passwords, secure email, reduce profile exposure, and treat breach-themed messages as.
Read article

Updated Mar 30, 2026
A recovery guide for mental health and healthcare breach notices: contain identity risk, freeze credit, watch for medical fraud, and reduce follow-on scams.
Read article
Updated Mar 30, 2026
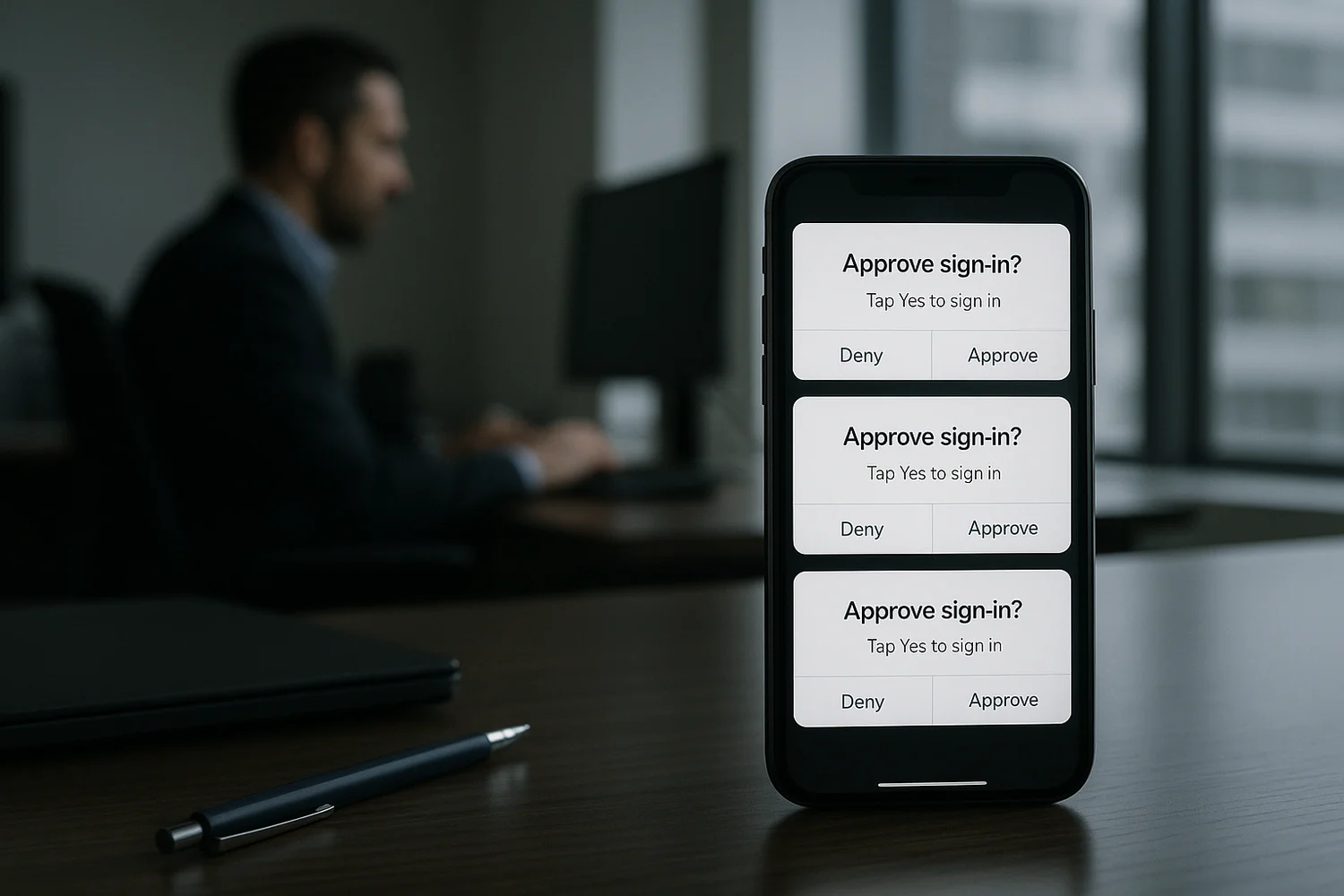
Repeated MFA prompts are a sign someone is trying to force an approval. Contain access, clean sessions, secure recovery channels, and harden MFA so prompts.
Read article
Updated Mar 30, 2026
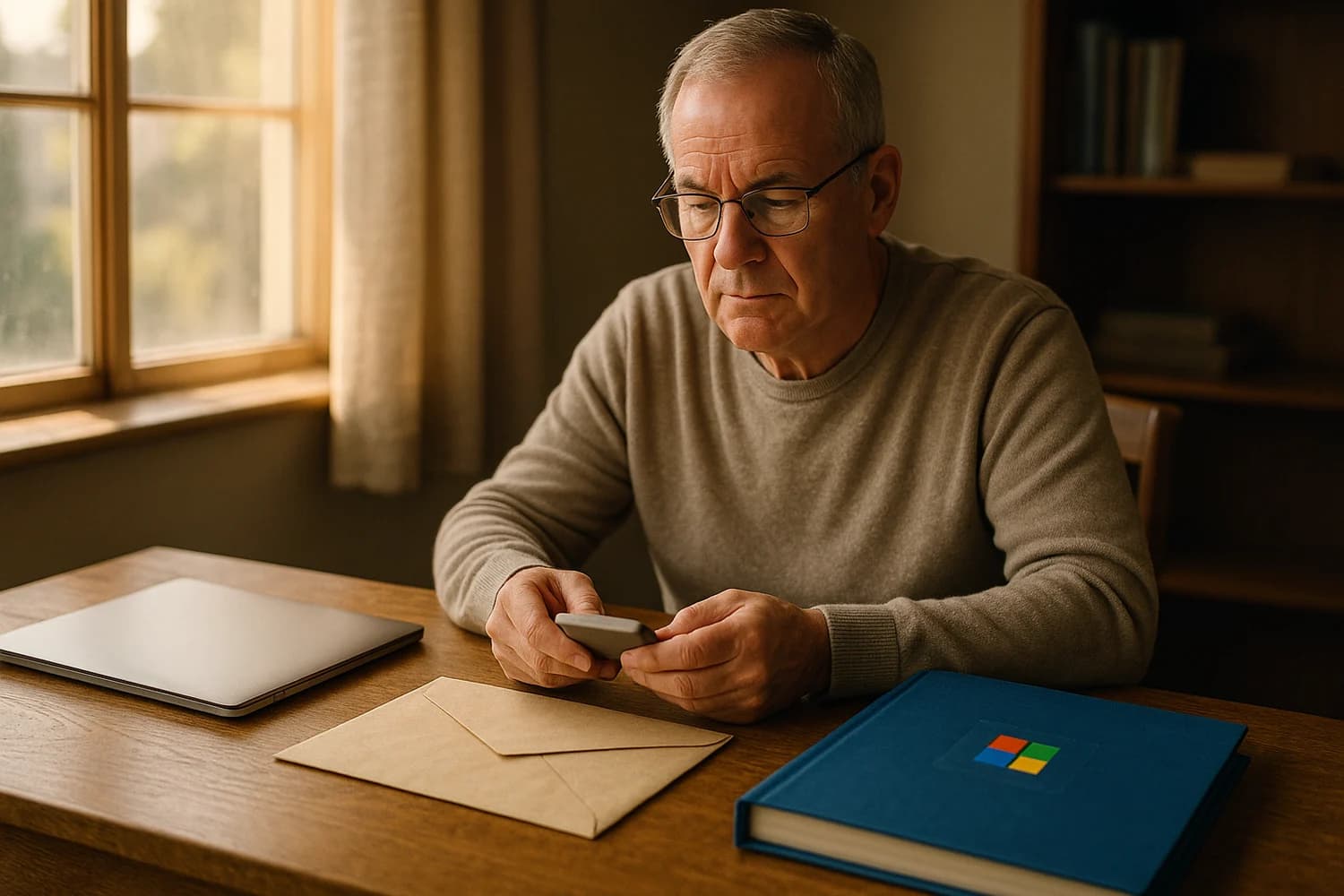
Understand what Microsoft allows after a death: account closure, inactivity timelines, legal-process limits on Outlook and OneDrive access, and OneDrive Digital
Read article

Updated Mar 30, 2026
The Exchange Server incident showed how patch lag scales. Use this checklist: patch, hunt for persistence, rotate credentials, reduce exposure, and enforce.
Read article

Updated Mar 30, 2026
Public account takeovers usually start with common failures: password reuse, phishing, weak recovery, or phone takeover. Use these operator-style controls to.
Read article

Updated Mar 30, 2026
Mac malware campaigns often steal sessions and credentials quietly. Learn how to contain access, verify device trust, clean safely, and prevent repeat.
Read article

Updated Mar 30, 2026
Smishing malware campaigns spread through fake delivery texts and app installs. Use this checklist to avoid link-based installs, secure accounts, and clean.
Read article

Updated Mar 30, 2026
Phishing emails pretending to be Meta or Instagram try to steal your login. Learn how to verify real Instagram security emails, recover if you clicked, and.
Read article
Updated Mar 30, 2026
High-profile indictments highlight repeatable tactics: phishing, password reuse, session persistence, and weak recovery controls.
Read article
Updated Mar 30, 2026
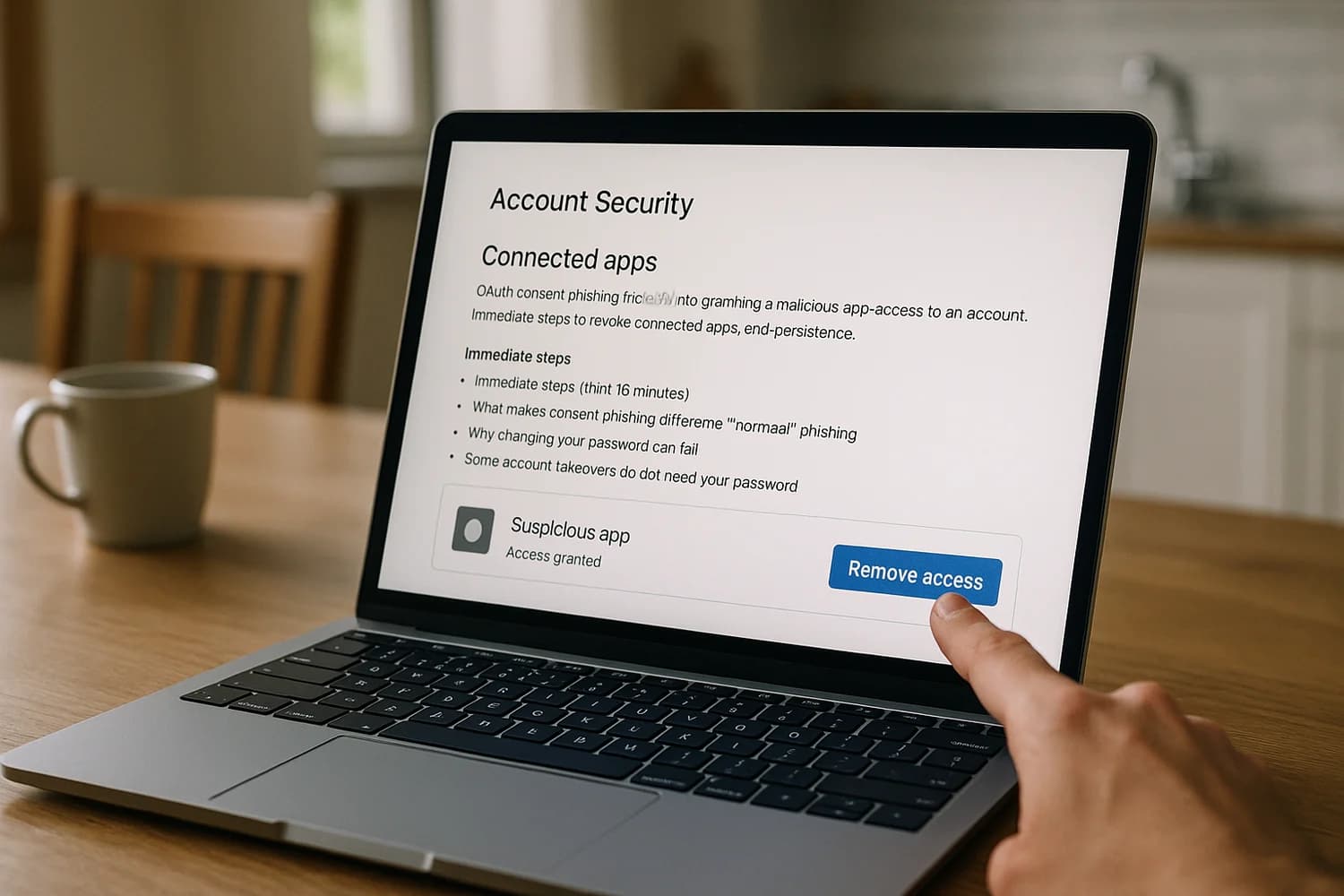
OAuth consent phishing tricks you into granting a malicious app access to your account. Learn the fastest way to revoke connected apps, end persistence, and.
Read article
Updated Mar 30, 2026
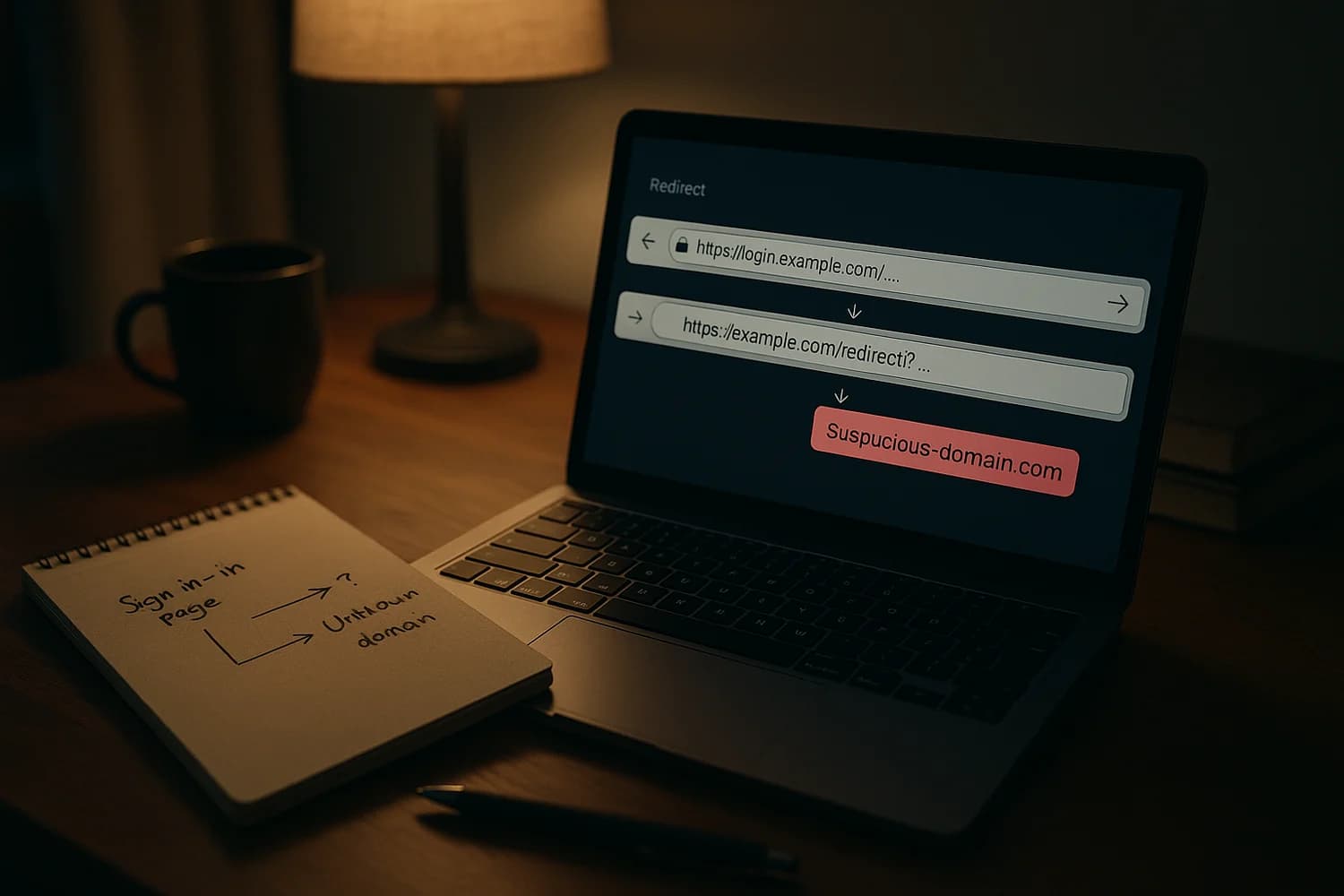
Attackers can start with a legitimate OAuth sign-in URL and still redirect you to a phishing page or malware. Learn what to do if you clicked, what to check in.
Read article

Updated Mar 30, 2026
Preparing for cybercrime is setting durable defaults: protect the control plane, upgrade authentication, patch exposed systems first, and make compromise visible.
Read article

Updated Mar 30, 2026
QR codes can hide phishing links in plain sight. Learn a verification workflow, high-risk scenarios, and what to do if you already scanned a malicious code.
Read article

Updated Mar 30, 2026
Ransomware spreads fast. Use this containment and recovery sequence to isolate systems, secure email and admin access, restore from trusted backups, and prevent
Read article

Updated Mar 30, 2026
If you got a Facebook password change email you did not request, verify it is real, contain access from a trusted device, revoke sessions, and secure recovery.
Read article

Updated Mar 30, 2026
A primary email change on Facebook usually means takeover. Verify the alert, secure the inbox, use facebook.com/hacked or the no-access recovery branch, remove.
Read article

Updated Mar 30, 2026
A business-first recovery playbook for Facebook Business Page and Meta Business Manager takeovers: containment in the first hour, proof preparation, and safe.
Read article

Updated Mar 30, 2026
Appeals failing? Learn how to recover a disabled Facebook account with documentation-first escalation, Meta support options, and California small-claims legal.
Read article

Updated Mar 30, 2026
Reduce public exposure that fuels impersonation and account takeover. Use this practical checklist to remove high-risk data, tighten visibility, and monitor drift.
Read article

Updated Mar 30, 2026
If you see an unknown Meta account linked in Facebook Accounts Center, treat it as persistence. Secure your inbox, remove unknown links, end sessions, and.
Read article

Updated Mar 30, 2026
AI makes phishing more convincing and scalable. Use these operator-grade decision rules, verification rituals, and control-plane protections to prevent fraud.
Read article

Updated Mar 30, 2026
Intrusions persist when privileges are broad and monitoring is weak. Use this boundary-first checklist to make compromise visible and containable.
Read article

Updated Mar 30, 2026
SIM swapping moves your phone number to an attacker so they can intercept SMS recovery codes and reset accounts. Use this containment-first playbook to stop the
Read article

Updated Mar 30, 2026
BitGrail’s reported Nano shortfall became a case study in exchange failure and disputed attribution. Learn the red flags, what to do during withdrawal freezes.
Read article

Updated Mar 30, 2026
Small businesses get hacked for predictable reasons: weak email security, password reuse, exposed remote access, and weak backups.
Read article

Updated Mar 30, 2026
Small claims court can be a last-resort escalation when Facebook/Meta account recovery fails. Learn when it’s appropriate, what happens after filing, what.
Read article
Updated Mar 30, 2026
If a company you used was hacked, the real risk is downstream: password reuse, phishing, and fraud. Use this step-by-step plan to secure accounts, reduce credit
Read article
Updated Mar 30, 2026
Seeing unreadable, encrypted Facebook emails? Use this recovery guide to verify whether it is a scam or PGP secure email, secure your inbox, regain access, and.
Read article

Updated Mar 30, 2026
A Facebook security warning can be benign or the start of a takeover. Verify the email, revoke unknown sessions, secure recovery methods, and prevent.
Read article

Updated Mar 30, 2026
Avoid common Craigslist scams: fake payments, overpayment refunds, shipping-only buyers, verification-code theft, and rental deposit fraud.
Read article

Updated Mar 30, 2026
Facebook ticket scams often use hacked accounts and hard-to-reverse payments. Verify ticket transfer paths, choose safer payment methods, and respond fast if.
Read article

Updated Mar 30, 2026
The 2022 threat landscape repeated the same failures: identity takeover, weak recovery, SaaS sprawl, and supply chain risk.
Read article

Updated Mar 30, 2026
Long-running intrusions thrive on weak visibility, patch lag, and credential sprawl. Learn the practical defenses that reduce dwell time: identity logging.
Read article

Updated Mar 30, 2026
Law enforcement crackdowns can shift attacker behavior, but they do not eliminate risk. Use this decision framework to harden identity, devices, and.
Read article

Updated Mar 30, 2026
Most successful compromises come from a few repeatable patterns: phishing, credential reuse, session theft, exposed remote access, and malware.
Read article

Updated Mar 30, 2026
Hacks create stress through loss of privacy and uncertainty. Contain the control plane first, preserve evidence, revoke sessions, and rebuild confidence with a.
Read article

Updated Mar 30, 2026
Facebook accounts are valuable for impersonation, ad fraud, and access to Pages and Groups. Learn the motives, takeover paths, and the controls that prevent.
Read article

Updated Mar 30, 2026
Choose a safer browser using durable criteria: update cadence, sandboxing, extension risk, and privacy controls. Includes a practical hardening checklist.
Read article