
Updated Mar 30, 2026
How to Secure Your Facebook Account
Secure the control plane that protects Facebook: inbox, 2FA, sessions, and integrations. A containment-first playbook to prevent persistence and business asset loss.
Read article
Knowledge Library
Explore account recovery, cyber safety, platform security, and incident response guidance from Hacked.com.

Updated Mar 30, 2026
Secure the control plane that protects Facebook: inbox, 2FA, sessions, and integrations. A containment-first playbook to prevent persistence and business asset loss.
Read article
Updated Mar 30, 2026
A leaked API key can enable silent access to cloud, CI, and SaaS. Learn how to revoke and rotate secrets, identify what was accessed, and harden your secret.
Read article

Updated Mar 30, 2026
A guide to the biggest bitcoin hacks and thefts: historical case studies, repeated failure modes, and the controls that reduce real-world loss risk.
Read article

Updated Mar 30, 2026
An update on the Elon Musk/Bill Gates Twitter bitcoin scam sentencing, with practical anti-scam and account security lessons that still apply.
Read article

Updated Mar 30, 2026
Camera compromises are usually access-control failures. Use this checklist to contain exposure, rotate credentials, audit users, and rebuild camera access with.
Read article

Updated Mar 30, 2026
YouTube Kids can reduce risk, but it is not a guarantee. Learn common failure modes and guardrails: content drift, search, time limits, and supervision habits.
Read article

Updated Mar 30, 2026
Major public events trigger predictable cyber scams. Learn verification habits, donation-check steps, and account hardening moves that reduce takeover and.
Read article

Updated Mar 30, 2026
Leaked offensive tools turn into mass exploitation when systems are exposed and patching lags. Use this boundary-first checklist to reduce blast radius and.
Read article

Updated Mar 30, 2026
If private photos were leaked, preserve evidence, start platform takedowns, secure email and cloud accounts, and close the access path to prevent re-entry and.
Read article

Updated Mar 30, 2026
Large incidents like the CNA event show the same failure modes: identity collapse, patch lag, and weak restores. Use this framework to contain and recover.
Read article

Updated Mar 30, 2026
Use Cybersecurity Awareness Month as a maintenance window: secure your inbox and admin accounts, adopt passkeys, patch critical systems, and test restores with.
Read article

Updated Mar 30, 2026
Security firms can be breached too. Learn the durable lessons from FireEye’s breach: control planes, tool theft risk, incident communications, and defensive.
Read article

Updated Mar 30, 2026
Geopolitical crises trigger phishing waves, donation fraud, and impersonation. Use this verification-first checklist to stay safe during attention spikes.
Read article

Updated Mar 30, 2026
Threat actor messaging is pressure management, not intelligence. Use this framework to contain access, verify restores, and harden identity and backups after.
Read article

Updated Mar 30, 2026
Ride-hailing apps collect sensitive location data. If you are concerned about cross-border processing, use a minimization plan: restrict permissions, reduce.
Read article

Updated Mar 30, 2026
Deepfake sexual imagery is a distribution and harassment problem. Preserve evidence, secure accounts, use platform takedown workflows, and reduce search.
Read article

Updated Mar 30, 2026
Understand what still blocks family access after death: passwords, passkeys, device encryption, provider policies, and why legacy tools do not replace a broader
Read article

Updated Mar 30, 2026
Personal account and device compromises create real work downtime. Learn the control-plane risks, high-leverage employee protections, and privacy-safe employer.
Read article

Updated Mar 30, 2026
After an EA security incident, phishing and credential-stuffing attempts spike. Secure your email, enable 2FA, harden linked platform accounts, and avoid fake.
Read article
Updated Mar 30, 2026
High-profile hacks usually come from ordinary failures: recovery compromise, SIM swaps, approval-based phishing, or stolen sessions.
Read article

Updated Mar 30, 2026
Recupera Facebook cuando te hackean: asegura tu correo, usa el flujo oficial, elimina sesiones del atacante, actualiza recuperacion y activa autenticacion fuerte.
Read article

Updated Mar 30, 2026
Pasos inmediatos si te hackearon: asegura tu correo, cierra sesiones, elimina acceso persistente, cambia contrasenas reutilizadas y activa autenticacion fuerte.
Read article

Updated Mar 30, 2026
A practical framework for evaluating antivirus vendor risk, switching safely, and reducing dependency on any one tool through stronger baseline controls.
Read article

Updated Mar 30, 2026
Facebook account recovery can be inconsistent. Reduce lockout risk by securing email, cleaning sessions, enabling stronger 2FA, and using official recovery.
Read article

Updated Mar 30, 2026
Infrastructure incidents repeat the same failures: exposed remote access, weak identity, shared admins, and untested recovery.
Read article

Updated Mar 30, 2026
After a platform hack, the real risk is follow-on credential stuffing and targeted phishing. Use this checklist to stop password reuse, secure email, and reduce
Read article

Updated Mar 30, 2026
Use the 2015 German Bundestag compromise as a case study: containment triggers, identity hardening, logging, segmentation, and incident response.
Read article
Updated Mar 30, 2026
Peloton devices are connected computers. Learn what the 2021 vulnerability reports meant, how to confirm you are patched, and the account and network steps that
Read article
Updated Mar 30, 2026
Leak-related news cycles trigger malware downloads and phishing. Use this checklist to avoid archive bait, verify sources safely, and secure accounts if you.
Read article

Updated Mar 30, 2026
Ransomware headlines usually share the same root causes: weak identity, exposed remote access, and weak backups. Learn the prevention baseline and the response.
Read article

Updated Mar 30, 2026
Public-sector ransomware incidents highlight the same defenses every organization needs: strong identity controls, reduced remote exposure, and tested backups.
Read article

Updated Mar 30, 2026
Hacking becomes legally risky when it crosses authorization boundaries. Learn common failure modes, safer alternatives, and how to disclose vulnerabilities.
Read article

Updated Mar 30, 2026
Use this diagnostic router to tell whether the failure is a Google sign-in problem, a Gmail-only mailbox issue, or a YouTube channel takeover, then jump to the.
Read article

Updated Mar 30, 2026
Targeted AI-driven scams are making impersonation, phishing, and fraud more convincing. Learn what TAIA means and the practical controls that stop it.
Read article

Updated Mar 30, 2026
Dark web price lists are volatile. Stabilize access, remove persistence, and harden the accounts that control password resets and payments.
Read article

Updated Mar 30, 2026
A practical way to evaluate kids games: chat/contact risk, spending, ads, permissions, and time. Includes safer defaults and an incident plan.
Read article

Updated Mar 30, 2026
The Facebook podcast scam steals Meta business access through role and integration requests. Learn the red flags, containment steps, and official recovery paths.
Read article

Updated Mar 30, 2026
Deepfake sexual abuse is often paired with account compromise and extortion. Reduce risk with exposure controls, inbox hardening, evidence discipline, and safe.
Read article

Updated Mar 30, 2026
Attackers target easy paths: exposed contact info, weak recovery, and password reuse. Reduce targeting pressure by securing email, hardening accounts, and.
Read article
Updated Mar 30, 2026
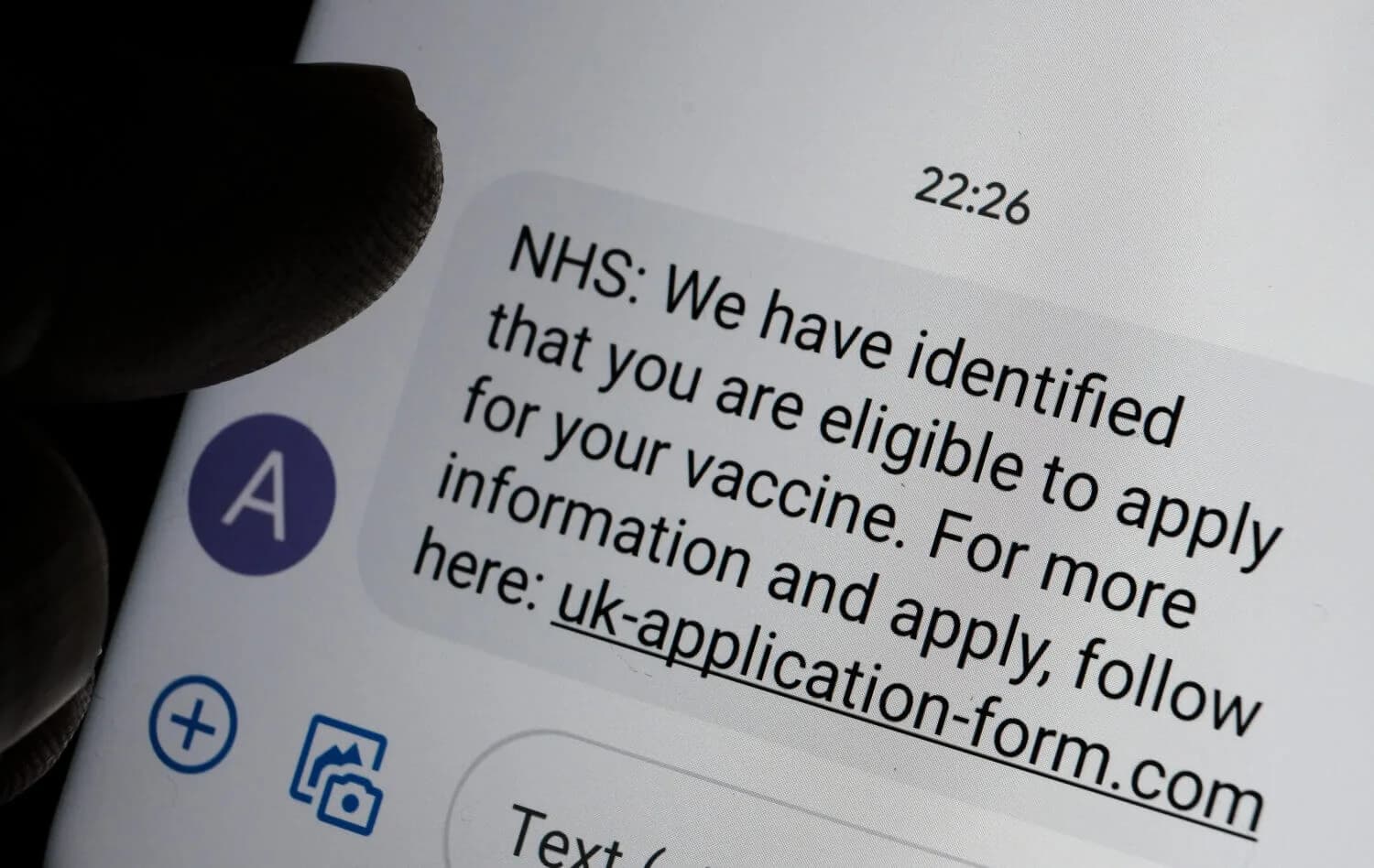
Text scams are optimized for speed. Use these rules to block code theft, delivery scams, and bank impersonation: no links clicked, no codes shared, verify in.
Read article

Updated Mar 30, 2026
Check for account takeover vs device compromise using high-signal indicators: new logins, password resets, account changes, and unauthorized charges.
Read article

Updated Mar 30, 2026
A practical response plan for abusive fans and harassment: preserve evidence, tighten contact surfaces, protect account recovery channels, and escalate safely.
Read article

Updated Mar 30, 2026
Delete Facebook photos, videos, and profiles safely without losing evidence you may need. Learn how to export your data, reduce exposure first, remove content.
Read article

Updated Mar 30, 2026
Turn on automatic App Store app updates on iPhone so security fixes install faster. Learn the Settings path, what each toggle controls, and why updates.
Read article
Updated Mar 30, 2026
A safe response sequence for online blackmail and extortion: stop escalation, preserve evidence, secure accounts, reduce distribution leverage, and use official
Read article
Updated Mar 30, 2026
File effective consumer or privacy complaints by building an evidence packet, choosing the right authority, and using official portals for fraud, identity.
Read article

Updated Mar 30, 2026
Hide old social posts safely by exporting your data first, securing your account, using archive and audience controls, and removing high-risk identifiers.
Read article

Updated Mar 30, 2026
Spot scam emails by focusing on the requested action, sender path, and verification routine. Learn how to check links and attachments safely, and what to do if.
Read article
Updated Mar 30, 2026
A universal privacy audit for social media: reduce discoverability, restrict inbound contact, control tags and location, audit connected apps, and keep accounts
Read article

Updated Mar 30, 2026
Most business compromises start with email, passwords, and remote access. Use this baseline: secure the control plane, reduce privileges, patch exposed systems.
Read article