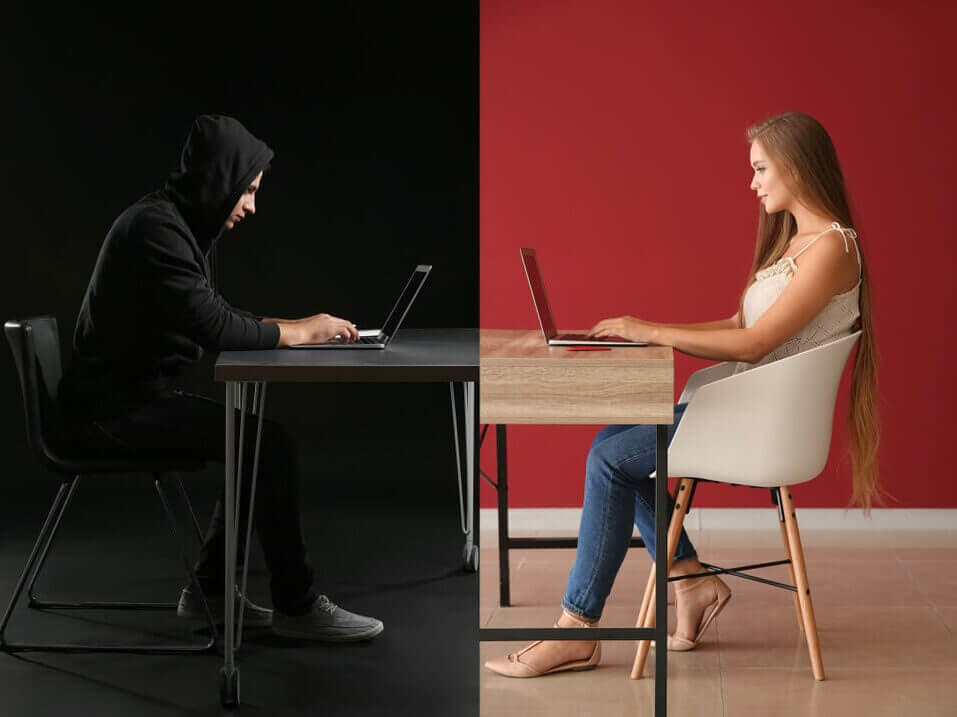
Dating-app breaches create two different risks at once. The first is account risk: attackers test reused passwords elsewhere. The second is social risk: profile data gives scammers material for targeted phishing, impersonation, and extortion pressure.
| First actions | Do this | Why |
|---|---|---|
| Stop reuse | Change reused passwords starting with your primary email | Password reuse turns one breach into many takeovers |
| Secure identity | Enable 2FA on email and key accounts | Email is the control plane for resets and alerts |
| Reduce exposure | Remove profile identifiers and limit cross-platform correlation | Limits impersonation and doxxing leverage |
| Expect scams | Treat breach-themed messages as hostile until verified | Scammers use breach context as credibility |
| Extortion | Do not pay and do not send more content; preserve evidence | Payment and engagement usually increase pressure |
Safety note: if someone threatens to expose private content unless you pay, treat it as extortion. Do not send money or more content, and preserve the messages.
What breach exposure means (and what it does not)
A breach can expose emails, usernames, profile content, and sometimes passwords or password hashes depending on what the company stored. Even when passwords are not exposed in plain text, scammers do not need your password to hurt you. They need a believable hook that makes you click a link, share a code, or panic.
Stop credential stuffing and account cascade
The most common technical harm after a breach is automated login testing on other services. If you reused the same password, assume it will be tested everywhere.
- Change passwords for any account that reused the same password or a similar pattern.
- Start with your primary email and your password manager, then move to financial and social accounts.
- Enable 2FA on the inbox and other high-value accounts.
If you want the mechanics in plain terms, see credential stuffing.
Expect targeted phishing and impersonation
Dating-app breach data is useful in scams because it creates personal pressure. Common patterns include:
- Messages that mention the app, your profile, or “leaked photos” to push you to a fake login page.
- Impersonation profiles that use your photos and name to contact friends or coworkers.
- Support scams that claim they can “delete the leak” or recover an account for payment.
For detection habits, use how to identify scam emails and phishing.
Key idea: breach data is used for social engineering. The attacker does not need to log in to hurt you, they need you to panic and comply.
Reduce profile exposure and cross-platform correlation
Exposure control is about removing the easy inputs attackers use to find you elsewhere.
- Remove identifiers from dating profiles: last name, workplace, school, and linked social handles.
- Avoid reusing the same username and profile photo across multiple platforms.
- If you are being targeted, tighten privacy settings on your main social accounts and remove public contact info.
Use reduce your digital footprint as a structured cleanup plan.
If photos or intimate content are being used for threats
Extortion threats are designed to make you move fast. The defensive move is to preserve evidence and work takedown and escalation channels without negotiating.
- Preserve messages, usernames, URLs, and timestamps.
- Do not pay and do not send more content.
- Use structured takedown workflows: remove non-consensual intimate images.
- If the content is being indexed, reduce discoverability: remove images from Google Search.
StopNCII is a victim-support service that helps participating platforms block reuploads of intimate images using hash matching without sharing the images themselves.
Check whether your email appears in known breach datasets
Use reputable breach notification services to check for known exposures, then treat any matches as a trigger to stop password reuse and harden recovery.
Escalation channels (US)
If the breach-driven follow-on includes extortion, hacking, or fraud attempts, reporting can be appropriate. Requirements vary by jurisdiction, so treat this as informational.
- FBI IC3 for internet-enabled scams and extortion attempts.
- If minors are involved or you suspect CSAM, use the NCMEC CyberTipline immediately.
- If you need immediate emotional support in the US, the 988 Lifeline is available.
Dating-app breach response is successful when the leaked data can no longer be used for account takeovers and when follow-on scams fail. That means unique passwords, strong authentication, and calm verification behavior. Once the account baseline is secure, focus on exposure control: minimize identifiers and avoid linking multiple profiles together. The goal is to reduce both technical risk and social pressure using the same discipline: verify, contain, and keep control of recovery paths.