
Updated Mar 22, 2026
How to Recover a Hacked Apple Account
Apple account recovery steps for Apple ID lockouts, suspicious iCloud activity, trusted-device cleanup, and account hardening after a takeover.
Read article
Knowledge Library
Explore account recovery, cyber safety, platform security, and incident response guidance from Hacked.com.

Updated Mar 22, 2026
Apple account recovery steps for Apple ID lockouts, suspicious iCloud activity, trusted-device cleanup, and account hardening after a takeover.
Read article

Updated Mar 22, 2026
Snapchat recovery steps for lockouts, suspicious snaps, email and phone cleanup, session removal, and protection against repeat takeovers.
Read article
Updated Mar 22, 2026
X account recovery steps for lockouts, suspicious posts, email and phone cleanup, app revocations, and protection against repeat takeovers.
Read article
Updated Mar 20, 2026
Targeted campaigns use impersonation, coercion, and account compromise to reach you and your contacts. Use this checklist to reduce exposure and recover safely.
Read article

Updated Mar 20, 2026
A practical Facebook hacked-account playbook: contain sessions, recover access using official flows, secure email/phone control planes, and stop repeat takeovers.
Read article

Updated Mar 20, 2026
Platform enforcement shocks can lock you out of pages and business assets. Learn how to protect access, preserve evidence, and reduce dependency risk.
Read article

Updated Mar 20, 2026
During high-alert periods, phishing and fraud spike. Use this surge playbook to cut risk with stronger authentication, verification rules, and session control.
Read article

Updated Mar 20, 2026
Why 2015-era breach data still causes harm today, and the practical steps that reduce account takeover and identity fraud risk.
Read article

Updated Mar 20, 2026
AI is improving fast, and that changes scams, impersonation, and fraud. Learn practical steps to prepare your accounts, data, and verification habits.
Read article

Updated Mar 20, 2026
Use this outage checklist to confirm Meta service issues safely, avoid outage-driven phishing, and recognize the signals that indicate account compromise.
Read article
Updated Mar 20, 2026
A mechanism map of 2021 cybercrime: identity collapse, patch lag, supply chain trust failures, and weak recovery. Use these controls to reduce impact.
Read article

Updated Mar 20, 2026
Small businesses are targeted because controls are inconsistent and access is broad. These five reasons map to practical fixes that reduce attacker leverage.
Read article

Updated Mar 20, 2026
The Capital One incident shows how cloud permissions and weak logging can turn into large data exposure and long-running legal risk. Learn the durable lessons.
Read article

Updated Mar 20, 2026
Most 'hackers for hire' are scams or create new risk. Use official recovery, incident response, and legitimate security help to regain control safely.
Read article

Updated Mar 20, 2026
CA AG consumer complaints can document harm, but they rarely restore hacked Facebook accounts directly. Learn what to do first and how to file a complaint safely.
Read article

Updated Mar 20, 2026
Telecom intrusions can expose metadata and enable follow-on targeting. Learn practical defensive moves: end-to-end encryption, inbox hardening, and number security.
Read article

Updated Mar 20, 2026
Security for small teams is resilience: protect the control plane, reduce blast radius, test restores, and assign owners so incidents stay containable.
Read article

Updated Mar 20, 2026
Small businesses face a few high-impact risks: phishing, password reuse, exposed remote access, and weak backups. Learn the baseline that cuts damage.
Read article

Updated Mar 20, 2026
Build a digital estate packet covering account maps, devices, trusted contacts, phone access, and password-manager instructions without creating new security risk.
Read article

Updated Mar 20, 2026
Prepare your digital legacy by organizing devices, trusted contacts, access plans, and legacy settings before illness or death creates lockout and confusion.
Read article

Updated Mar 20, 2026
Set up Facebook legacy contact and memorialization so family can manage a memorialized profile, request deletion, and avoid mistaken assumptions about access.
Read article

Updated Mar 20, 2026
Handle a deceased family member's Google Account by separating closure, content review, and pre-planned Inactive Account Manager access without guessing.
Read article

Updated Mar 20, 2026
Request access to a deceased family member's Apple Account by choosing the Legacy Contact route or legal-document path and understanding what Apple still blocks.
Read article

Updated Mar 20, 2026
Ransomware is an outage and breach risk. Learn first-hour actions, common entry points, and controls like MFA and backups that change recovery outcomes.
Read article

Updated Mar 20, 2026
After Colonial Pipeline, TSA pipeline rules pushed faster reporting, named cyber ownership, and baseline controls. Learn what operators must prove.
Read article

Updated Mar 20, 2026
Ransomware extortion response: first-hour actions, decision points, safe restoration, and controls that reduce repeat compromise and legal risk.
Read article
Updated Mar 20, 2026
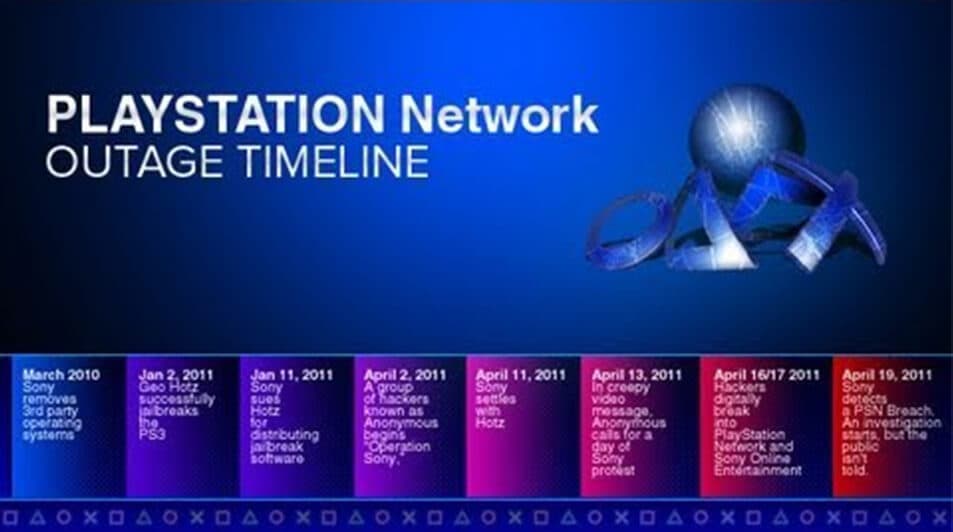
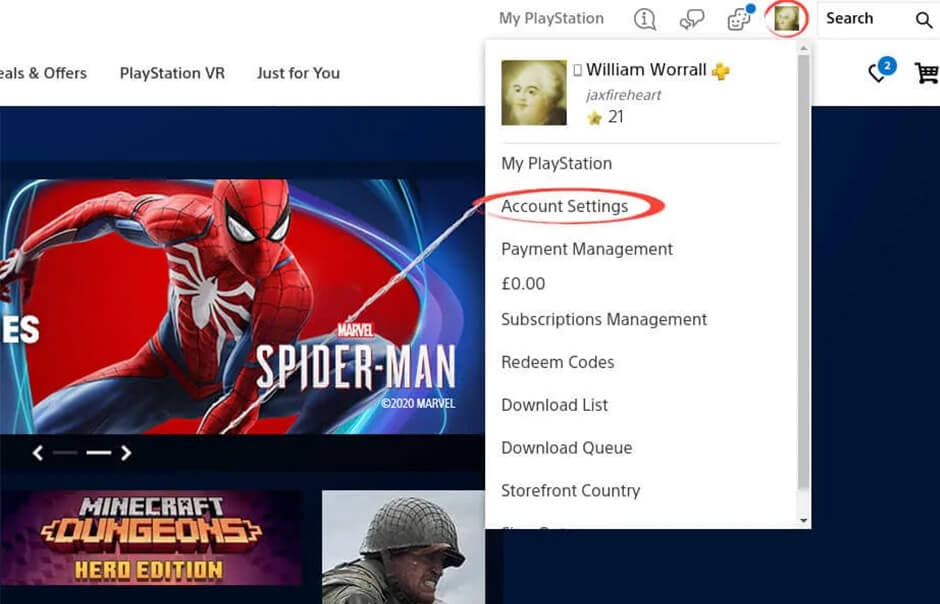
PSN security is about what you can control: inbox security, 2-step verification, session reviews, and purchase controls that reduce takeover risk.
Read article
Updated Mar 20, 2026
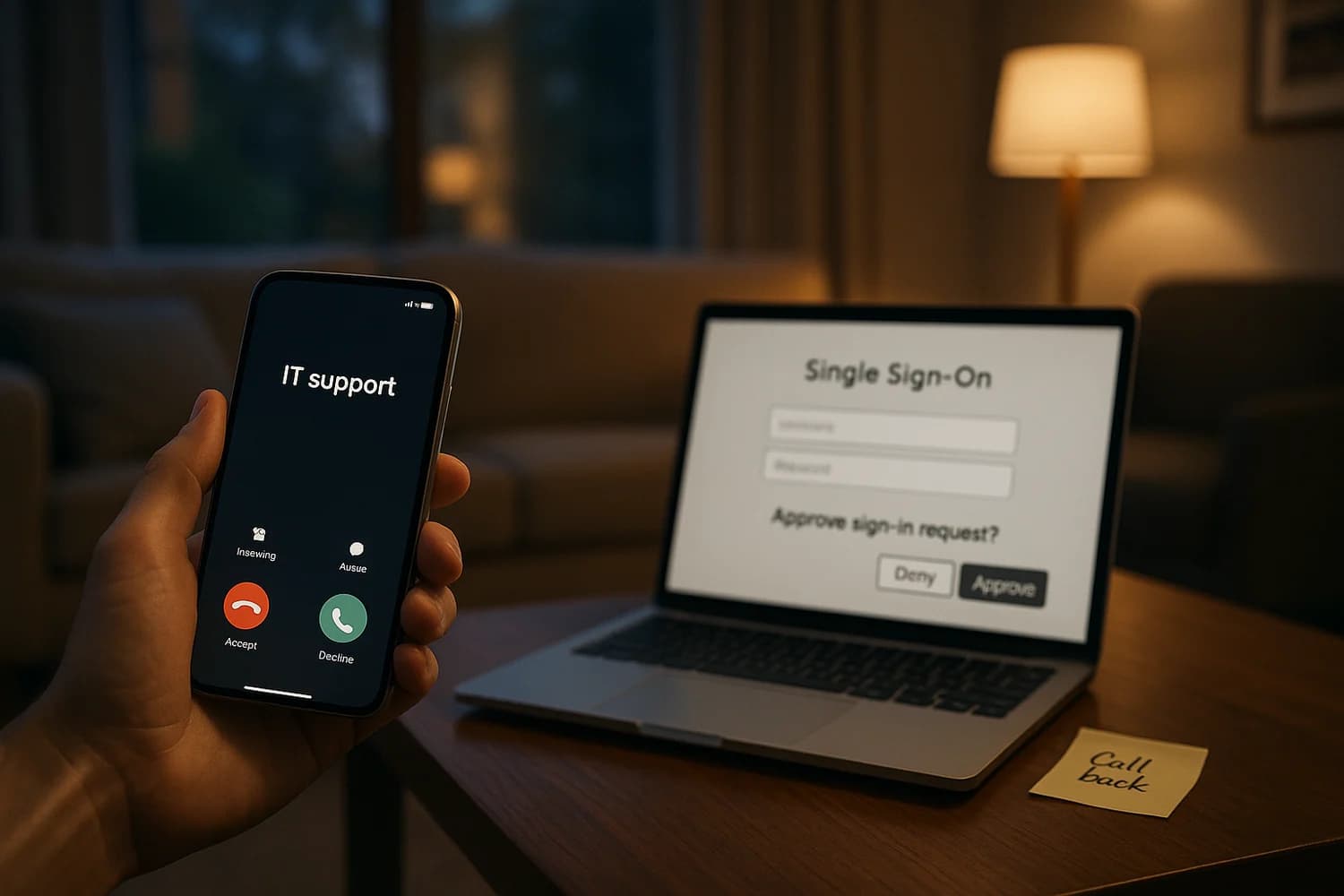
Vishing kits steer SSO logins and MFA prompts in real time. Learn what to do if you shared a code, approved a prompt, or suspect a helpdesk bypass.
Read article

Updated Mar 20, 2026
Verify a grandkid ransom call, spot cloned voices and fake proof-of-life images, contain payment risk, and report virtual kidnapping scams fast.
Read article
Updated Mar 20, 2026
Apple Legacy Contact: who can access your data, what stays blocked, what the access key does, and how to fit it into a family digital legacy plan.
Read article

Updated Mar 20, 2026
Been hacked? Secure email and phone first, clean devices, end attacker sessions, rotate passwords safely, and preserve evidence before re-entry starts again.
Read article

Updated Mar 20, 2026
Google Inactive Account Manager lets you choose trusted contacts, shared data, and account deletion after inactivity so your family is not left guessing.
Read article

Updated Mar 20, 2026
Recover your hacked Facebook account: contain first, facebook.com/hacked + login/identify, email changed, attacker 2FA, disabled accounts, business takeover.
Read article
Updated Mar 19, 2026
Spyware signs are often subtle. Use this checklist to diagnose, contain, and remove spyware without falling for fake “spyware removal” scams.
Read article

Updated Mar 19, 2026
Outlook and Microsoft 365 security checklist: remove mailbox-rule persistence, revoke sessions, harden 2FA, and prevent repeat compromise.
Read article

Updated Mar 19, 2026
If your phone number or email was exposed in a large Facebook-related leak, attackers use it for phishing and SIM swap targeting. Here is a practical defense plan.
Read article

Updated Mar 19, 2026
What deepfakes are, why they are dangerous, how they are used in scams, and the practical verification steps that keep you safe.
Read article
Updated Mar 19, 2026
After a data breach, secure the accounts that can reset everything, stop fraud early, and harden recovery paths. Use this time-based checklist to respond safely.
Read article

Updated Mar 19, 2026
A practical ransomware incident-response playbook: what to do in the first 30 minutes, how to contain spread, how to restore safely, and how to prevent a repeat.
Read article

Updated Mar 19, 2026
Do you know the signs of a hacked iPhone or Android phone? Learn what you should do if your smartphone is in fact hacked.
Read article

Updated Mar 19, 2026
Secure Instagram by locking down email, choosing a stronger 2FA method, reviewing login activity, checking Accounts Center, and reducing impersonation risk.
Read article

Updated Mar 19, 2026
Delete an email account without breaking logins: export data, move resets, remove forwarding, and secure the accounts that depend on that inbox.
Read article

Updated Mar 19, 2026
A safe, repeatable workflow for deleting or deactivating social media accounts: data export, unlink logins, remove recovery risk, and reduce search exposure.
Read article

Updated Mar 19, 2026
Recover a hacked Steam account by securing email, cutting off sessions, reviewing trade and market abuse, revoking API access, and cleaning compromised devices.
Read article

Updated Mar 19, 2026
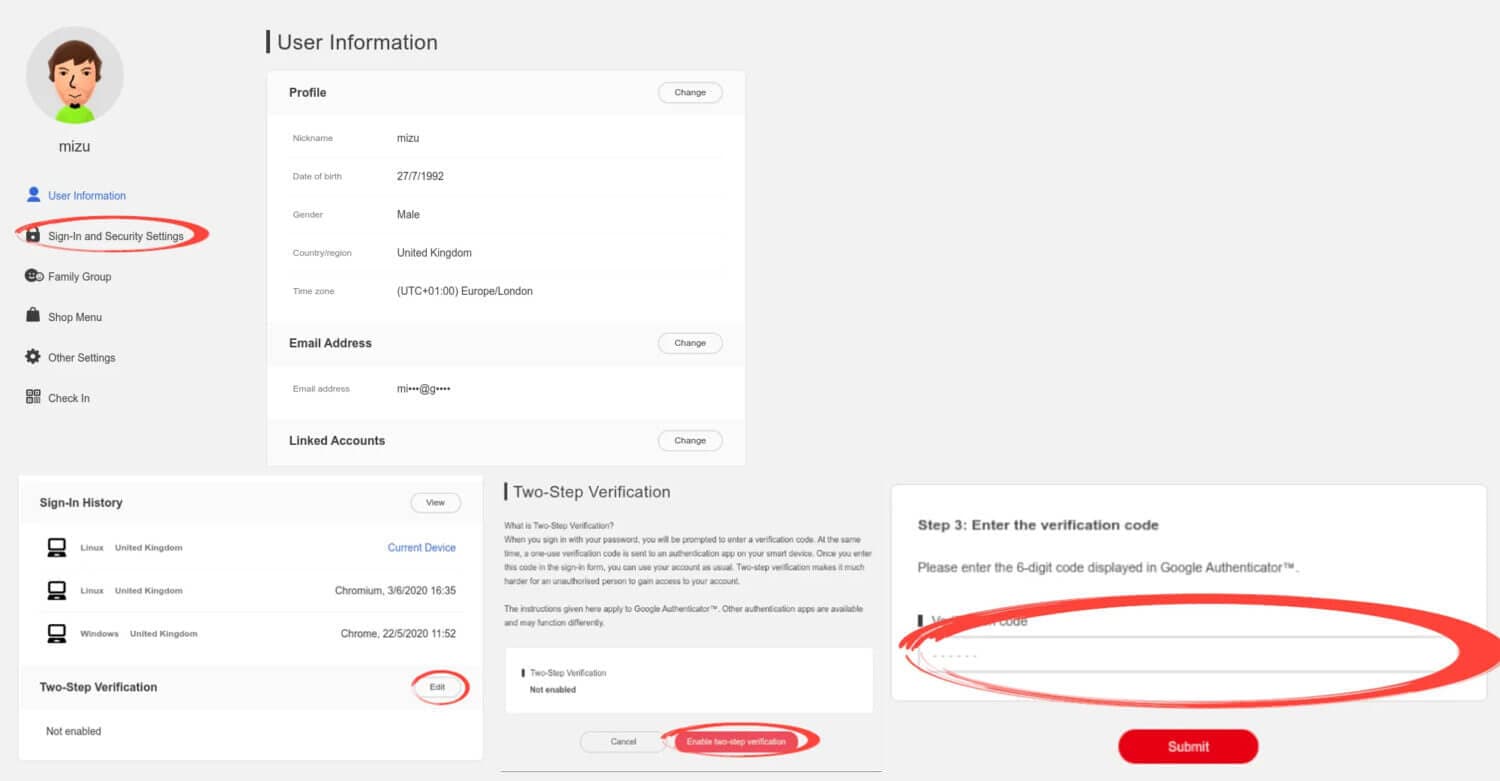
Recover a hacked Nintendo Account: secure email, stop unauthorized eShop charges, repair family-group fallout, and lock down 2-step verification.
Read article

Updated Mar 19, 2026
Recover a hacked AOL account by using Sign-in Helper, fixing recovery info, removing suspicious activity and app passwords, and avoiding fake AOL support scams.
Read article
Updated Mar 19, 2026
If Facebook disabled a hacked account, secure the inbox, preserve evidence, follow the review flow, and separate takeover recovery from enforcement.
Read article
Updated Mar 9, 2026
A practical Nintendo Account security checklist: unique password, 2FA, recovery hygiene, purchases, devices, and what to do if you suspect compromise.
Read article
Updated Mar 9, 2026
Secure your PSN account with a practical checklist: unique passwords, 2-step verification, email hardening, purchase controls, and anti-scam habits.
Read article
Updated Mar 9, 2026
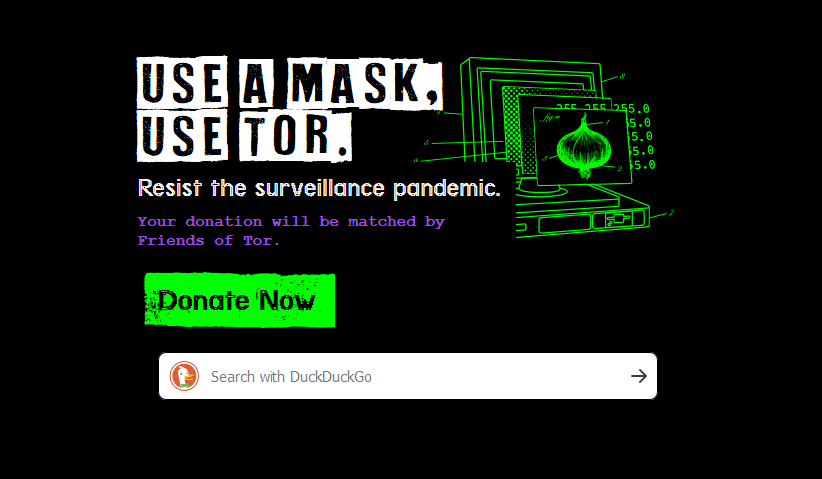
Understand the dark web vs the deep web, how criminals use it to trade stolen credentials and run scams, and what to do defensively if your data is exposed.
Read article