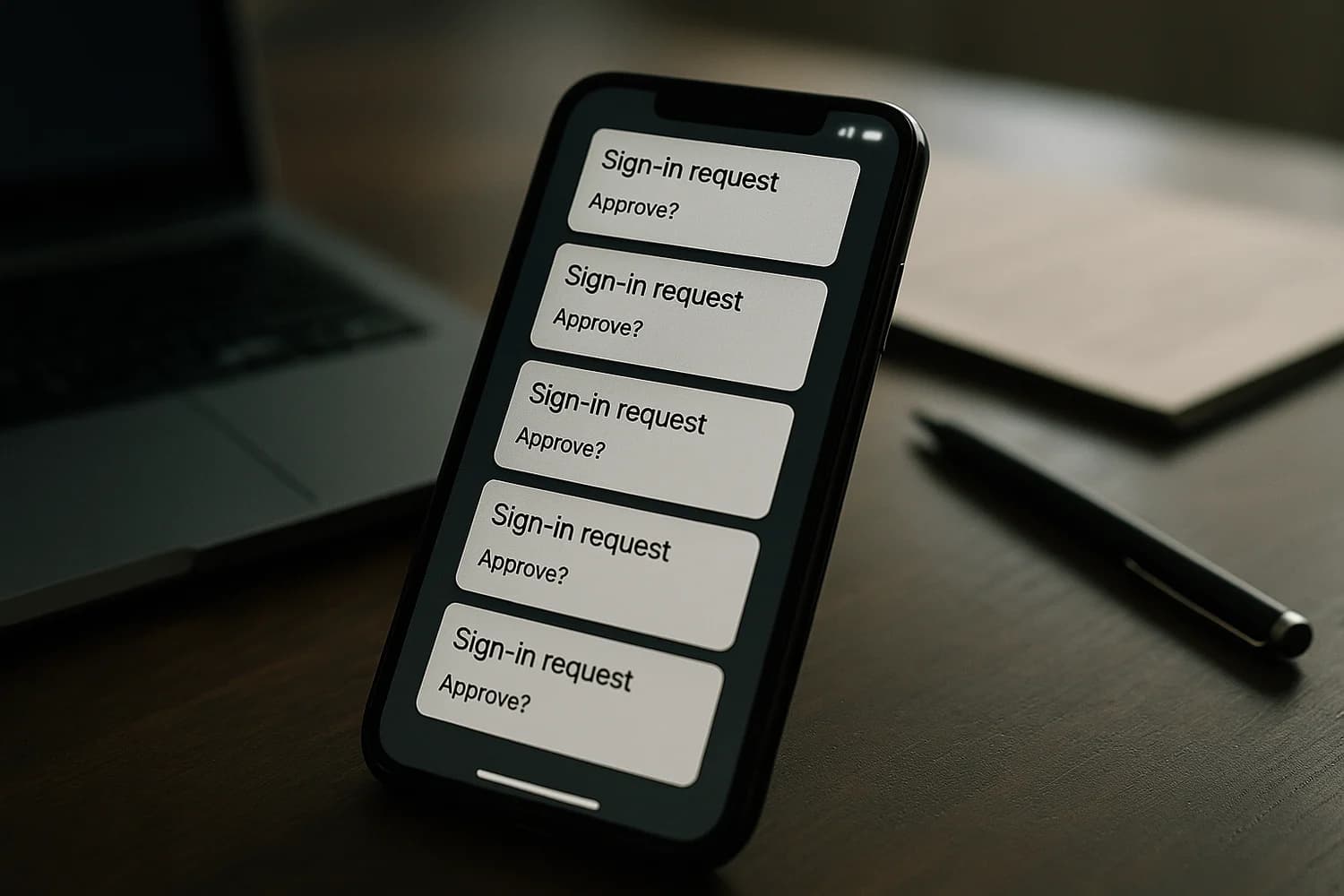
MFA fatigue (sometimes called push bombing) is when an attacker repeatedly triggers multi-factor authentication prompts, hoping you approve one out of frustration, confusion, or time pressure.
Approval-based prompts can turn a small mistake into full account access, especially if the attacker already has your password.
Why it matters for account recovery
Repeated push prompts are often a live compromise signal. If a prompt is arriving and you did not initiate it, treat the account as actively under attack and assume the attacker is trying to establish a stable session.
Common failure modes and misconceptions
- Thinking prompts are harmless: A single 'Approve' can be enough to create an authenticated session that persists after you stop seeing prompts.
- Relying on push-only MFA: Push is convenient, but it is also a social engineering surface. Attackers exploit notification fatigue.
- Ignoring the follow-on steps: If prompts stop, it does not mean the attack stopped. It can mean the attacker succeeded.
Safe best practices
- Deny unexpected prompts and use report options when available.
- Change the password from a trusted device, sign out of other sessions, and review security info for changes you did not make.
- If your provider supports number matching, a code challenge, or other prompt context, turn it on so approvals are harder to fake or rush.
- Move to stronger authentication that resists approval mistakes, such as passkeys or security keys, where supported.
- Review recovery methods so the attacker cannot reset access later.
Related terms
Related guides
- MFA fatigue attacks (push bombing): how to stop approval-based account takeovers
- Can two-factor authentication be hacked?
- How to recover a hacked Instagram account
- How to secure Outlook and Microsoft 365 accounts
When MFA is treated as a decision you make deliberately, not a notification you clear quickly, fatigue attacks stop working. The goal is fewer approvals, stronger methods, and faster response when something feels off.